Leverage Cloud Solutions for Enhanced Data Safety And Security
In today's digital landscape, the ever-evolving nature of cyber threats necessitates a proactive technique in the direction of securing sensitive information. Leveraging cloud solutions provides an engaging solution for organizations seeking to strengthen their data security procedures. By turning over trusted cloud service companies with information management, organizations can touch into a riches of protective attributes and innovative modern technologies that boost their defenses versus harmful stars. The question arises: exactly how can the usage of cloud services reinvent information safety and security techniques and supply a durable shield versus potential vulnerabilities?
Relevance of Cloud Safety And Security
Ensuring durable cloud protection procedures is critical in guarding sensitive data in today's electronic landscape. As organizations progressively depend on cloud solutions to keep and refine their information, the requirement for strong safety methods can not be overstated. A violation in cloud safety and security can have serious repercussions, varying from monetary losses to reputational damage.
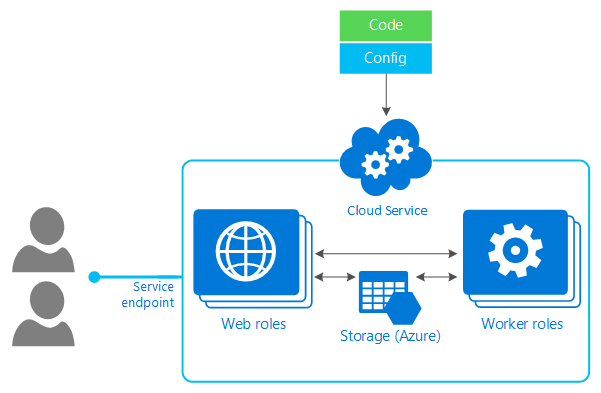
Among the main reasons cloud security is important is the common responsibility version utilized by a lot of cloud provider. While the service provider is accountable for protecting the infrastructure, customers are accountable for safeguarding their data within the cloud. This division of duties emphasizes the value of executing durable safety procedures at the customer level.
In addition, with the expansion of cyber hazards targeting cloud environments, such as ransomware and information breaches, companies need to stay positive and cautious in mitigating threats. This includes frequently upgrading safety methods, checking for suspicious activities, and enlightening workers on ideal techniques for cloud safety and security. By prioritizing cloud protection, organizations can better protect their sensitive information and maintain the trust of their stakeholders and consumers.
Data Encryption in the Cloud
Security in the cloud commonly involves the usage of cryptographic algorithms to clamber data into unreadable formats. This encrypted information can just be understood with the matching decryption key, which adds an extra layer of protection. In addition, many cloud service carriers offer encryption devices to protect data at remainder and en route, boosting total data protection. Applying robust file encryption methods together with other protection measures can significantly bolster a company's protection against cyber threats and safeguard useful info saved in the cloud.
Secure Data Backup Solutions
Information back-up services play a critical role in guaranteeing the durability and security of information in case of unanticipated incidents or data loss. Protected data backup options are important parts of a durable information security technique. By routinely backing up information to safeguard cloud web servers, companies can alleviate the risks connected with data loss because of cyber-attacks, hardware failures, or human error.
Implementing protected information backup services entails picking dependable cloud solution companies that provide security, redundancy, and information stability steps. In addition, information integrity checks ensure that the backed-up data stays tamper-proof and unchanged.
Organizations needs to develop automatic backup timetables to make sure that data is regularly and efficiently backed up without manual intervention. Regular screening of information restoration procedures i loved this is additionally essential to ensure the effectiveness of the backup solutions in recouping information when needed. By spending in secure data backup options, organizations can enhance their data safety and security stance and reduce the impact of potential information breaches or disturbances.
Duty of Accessibility Controls
Executing strict accessibility controls is vital for keeping the security and stability of sensitive details within organizational systems. Gain access to controls serve as a crucial layer of defense against unauthorized access, guaranteeing that only authorized individuals can watch or manipulate sensitive information. By specifying that can gain access to particular sources, organizations can limit the danger of data violations and unapproved disclosures.

Routinely upgrading and assessing accessibility controls is necessary to adjust to business modifications and evolving safety and security risks. Continual surveillance and bookkeeping of access logs can assist find any questionable activities and unauthorized accessibility efforts immediately. On the whole, durable access controls are basic in protecting delicate information and mitigating safety dangers within organizational systems.
Compliance and Laws
Frequently ensuring conformity with appropriate policies and standards More hints is vital for organizations to support data safety and personal privacy steps. In the world of cloud solutions, where information is commonly stored and refined externally, adherence to industry-specific guidelines such as GDPR, HIPAA, or PCI DSS is essential. These laws mandate particular information handling techniques to safeguard delicate info and ensure customer privacy. Failing to comply with these regulations can lead to serious penalties, including penalties and lawsuits, harming an organization's credibility and trust.
Cloud provider play a vital role in aiding organizations with conformity initiatives by providing solutions and functions that line up with various governing needs. For circumstances, many companies use file encryption capabilities, access controls, and audit trails to help organizations you could check here meet data safety and security criteria. In addition, some cloud solutions undergo regular third-party audits and qualifications to demonstrate their adherence to industry regulations, supplying included assurance to organizations looking for compliant services. By leveraging compliant cloud solutions, organizations can enhance their information security stance while satisfying regulative obligations.
Conclusion
Finally, leveraging cloud services for enhanced information safety and security is necessary for companies to shield delicate info from unauthorized access and prospective violations. By carrying out durable cloud security methods, consisting of information file encryption, protected backup solutions, gain access to controls, and conformity with policies, organizations can take advantage of advanced security procedures and expertise supplied by cloud company. This assists mitigate dangers efficiently and guarantees the confidentiality, stability, and availability of information.

Information back-up options play an essential function in ensuring the durability and security of data in the occasion of unforeseen cases or data loss. By regularly backing up information to protect cloud web servers, organizations can reduce the threats associated with data loss due to cyber-attacks, equipment failures, or human error.
Applying protected information backup services entails selecting dependable cloud solution providers that supply encryption, redundancy, and data integrity procedures. By investing in safe and secure data backup services, businesses can improve their information safety posture and decrease the impact of prospective data breaches or disturbances.